Configuration and Deployment of MOM Agents
When planning to configure and deploy MOM agents, the first step in the deployment process is to identify and make a record of the computers that you want to manage by using MOM. All of these computers must meet the requirements listed in the Microsoft Operations Manager 2005 Supported Configurations documentation.
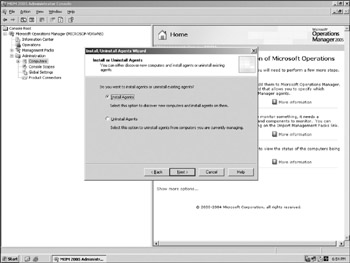
To install agents, an administrator has several options. There is a wizard supporting the installation process along with command line support. Let's look at the steps involved in using the Install/Uninstall Agents Wizard, shown in Figure 7-1, to install agents on computers in your Management Group. You can add computers to any Management Server in the Management Group by running the Install/Uninstall Agents Wizard. The Management Server that you select will be the primary Management Server for the managed computers on which you install agents. To install an agent, you need to perform the following steps:
-
In the MOM Administrator Console, click the root, and then select the Administration or Computers node.
-
In the Detail pane, click Install/Uninstall Agents Wizard.
-
If you have more than one Management Server in the Management Group, the Select Management Server page appears. Select a Management Server from the list, and then click Next.
-
If you have previously installed agents on the selected Management Server, the Install or Uninstall Agents page appears. Leave the Install Agents option selected, and then click Next.
-
On the Method for Discovering Computers and Installing Agents page, click Browse for or type in specific computer names, or click Search Criteria, and then click Next.
-
If you selected the Browse for or type in specific computer names option in Step 5, complete the following steps:
-
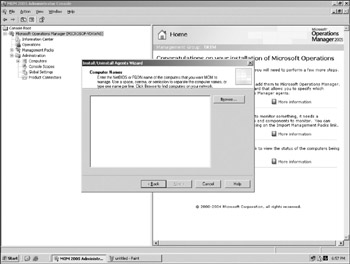
On the Computer Names page, click Browse to locate computers on your network (see Figure 7-2), or type the names of computers on which you want MOM to install agents. You can use fully qualified domain names or NetBIOS names. If you're running Active Directory, you should use fully qualified names. If you use NetBIOS names, MOM automatically contacts each of those computers to verify that they exist. This can slow down the computer discovery process.
-
-
If you selected Search Criteria in Step 5, you'll need to complete the following steps:
-
On the Computer Discovery Rules page, click Add.
-
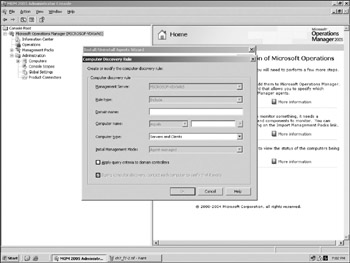
In the Computer Discovery Rule property dialog box, specify the rule properties (see Figure 7-3). You can create a rule to include or exclude a computer or group of computers with this rule. The rule depends on Computer Name, and there are options to find a name that equals a value. Other options allow you to search for a substring, match a wildcard, or evaluate a regular expression or a Boolean expression. Note that discovery rules relying on regular expressions could have some negative performance because of additional resources being allocated during this type of discovery.
-
Repeat the previous two steps for each computer or group of computers on which you want to install agents.
-
Select Next and proceed to Step 8.
-
-
On the Agent Installation Permissions page, leave the Management Server Action Account selected, or select Other and type a user name and password for the account. The account you select must have administrative credentials on all computers where you're installing agents.
-
On the Agent Action Account page, leave the Local System option selected, or select Other and type a user name and password for the account.
-
On the Agent Installation Directory page, type the local directory where the MOM agent will be installed on the targeted computers. The default directory is ProgramFiles\Microsoft Operations Manager 2005. Select Next.
-
On the Completing the Install page of the Uninstall Agents Wizard, review your selections. If you want to monitor the agent installation progress, select the Show task progress check box, and then select Finish.
With MOM agent installations, you need to consider the security aspects of agent deployment. Agent installation, or deployment, involves a few security requirements and some security considerations. You can choose the security context that the agent runs under. You can deploy agents automatically by creating computer discovery rules, or manually by using the Agent Installation Wizard on the remote computer.
When you use the Install/Uninstall Agents Wizard, MOM searches for and installs agents on computers on your network. The MOM Management Server performs a computer discovery based upon the criteria that you specify in the wizard and always installs (or uninstalls) the agents regardless of the setting on the Automatic Management tab of the Management Server properties. When the Management Server discovers new computers, it either installs agents or puts the computers in the Pending Actions folder, depending upon the setting on the Automatic Management tab of the Management Server properties.
If you are using discovery-based agent deployment, you can either provide credentials for an account, or you can use the Management Server's action account. The account you use must be a local administrator on all of the computers to which you are deploying agents. The credential information that is used to install agents is encrypted before being communicated and then discarded after use. The Management Server's action account can be used for installing or uninstalling agents on remote computers and updating settings on agents. If you choose to use the account for this purpose, the account must be a domain account with administrator privileges on all target computers to which it is to install agents. An alternative to using this highly privileged account is to configure the Management Server's action account to be a low-privileged account and to either specify credentials for installing agents when you use the Install/Uninstall Agents Wizard, or manually install agents.
The Management Server uses the following to deliver the files needed for agent installation on remote computers and for updating agent settings after installation:
-
The Server Message Block (SMB) port (445/TCP)
-
The RPC port (135/TCP)
-
The DCOM port range
If these ports are disabled on the Management Server or any of the target computers, or the target computer and Management Server are separated by a firewall, you cannot use discovery-based deployment to install agents. You must either enable these ports or install the agents manually. Manual installation does not require these ports. If you disable the File and Printer Sharing for Microsoft Networks and the Client for Microsoft Networks services, the SMB ports are disabled as well. Because of these security implications related to MOM agent deployment, MOM agents must be manually installed or updated under the following circumstances:
-
The agent and Management Server are separated by a firewall.
-
The agent is running MOM 2000 (the agent must be either manually removed and a MOM 2005 agent installed, or the agent must be upgraded to a MOM 2000 SP1 agent before upgrading to a MOM 2005 agent).
-
The agent cannot be installed on a computer running Microsoft Windows NT 4.0.
-
The agent cannot be installed on a Microsoft Cluster Services virtual server. You can install an agent on a physical node.
In some cases, you may find it necessary to manage a computer outside of a firewall. You can have normal communications between managed computers that are beyond a firewall from the Management Server if you open the TCP/UDP port 1270. However, you must manually install and update these agents. Mutual authentication and the signed and encrypted communications are still available if a full Active Directory trust relationship exists between the Management Server domain and the agent domain. Otherwise only signed and encrypted communications are available.
You can also have agents in non-trusted domains or workgroups; however, mutual authentication is not available because, by definition, no two-way trust relationship exists between the Management Server domain and the agent domain. The secure channel is still available, however. You must install and update the agents manually. If the Management Server is configured to require mutual authentication, these agents will not be able to communicate with it. By default, MOM does not secure the files and other data that are used to deploy agents. The deployment process uses both the SMB ports and the RPC/DCOM port range. You can use either SMB packet signing or IPSec to secure the agent deployment.
In the case of a manual agent deployment, there are command-line options available when installing a MOM agent by using the Agent Setup Wizard (MOMAgent.msi). The command-line options are shown in the following table.
|
Option |
Description |
|---|---|
|
INSTALLDIR |
The destination folder for installing the agent. The default value is ProgramFiles \Microsoft Operations Manager 2005. |
|
CONFIG_GROUP |
The Management Group name. |
|
MANAGEMENT_SERVER |
The primary Management Server for the agent. |
|
ADD_CONFIG_GROUP |
Used to add the agent to another Management Group for mul-tihoming. |
|
AM_CONTROL |
The agent control level: either Full or None. |
|
ACTIONSUSER |
The user name for the MOM Agent Action Account, if you want to use an account other than the default Local System account. |
|
ACTIONSPASSWORD |
The password for the MOM Agent Action Account, if you want to use an account other than the default Local System account. |
|
ACTIONSDOMAIN |
The domain of an account to use for the MOM Agent Action Account if you want to use an account other than the default Local System account. |
|
CHANGE_CONFIG_GROUP |
Used to change the agent Management Group. Set this value to 1, and then indicate the Management Group using the CON-FIG_GROUP option. |
|
REMOVE_CONFIG_GROUP |
Used to remove an agent from a Management Group. Set this value to 1, and specify the Management Group for removal by using the CONFIG_GROUP option. When the last Manage-ment Group is deleted from the agent configuration, the agent is uninstalled. |
|
SECURE_PORT |
The secure port to use for agent communication. The default value is 1270. |
|
REQUIRE_AUTH_COMMN |
Enables mutual authentication. To enable mutual authentica-tion, set this value to 1. If this value is set to zero, mutual authentication is not used. The default value is zero. |
|
ALT_MANAGEMENT_SERVER |
Another Management Server in the same Management Group. The agent contacts this Management Server only if the primary Management Server (MANAGEMENT_SERVER) is unavail-able during the installation process. |
Here's an example of an agent with control level of None installed in the default location using a domain account for the MOM Agent Action Account.
msiexec /qn /I \\[location of setup program]\MOMAgent.msi CONFIG_GROUP="group_name" MANAGEMENT_SERVER="server_name" AM_CONTROL="None" ACTIONSUSER="account_name" ACTIONSPASSWORD="account_password" ACTIONSDOMAIN="domain_name"
While agents are important in the MOM architecture, it is possible to perform some of the monitoring functions without the use of an agent. This is called agentless monitoring, and it describes the ability to monitor remote resources in a manner that is similar to how local resources are monitored through providers and responses in the local agent scenario. If providers that support remote access to resources are used and the responses can execute its logic remotely using tools such as RPC or DCOM, then those sets of rules work the same way on both agentless and agent-managed computers. Once a computer is identified, MOM starts monitoring the agentless computer as though there were an agent installed on the computer.
You need to think about a few things before opting for agentless monitoring. First, the MOM Action Account must have administrative user rights on the computers you want to manage without an agent. So while there is less intrusion because there is no installed agent, the privileges required could be considered to be intrusive from a security perspective. As discussed in Chapter 2, administrators can achieve the following with agentless monitoring:
-
State monitoring.
-
Heartbeat: The MOM Management Server pings the agentless computer at intervals specified by the user. If no response is received, an alert is raised for the Unavailable computer.
-
Performance collection: Microsoft Windows NT performance counter and script-generated.
-
Internal service monitoring events.
-
Script execution: Including varsets.
-
Event collection: Timed, Windows Event Log, WMI, internally generated, and script-generated.
However, agentless monitoring has the following limitations:
-
It does not support application log providers.
-
Descriptions of event log entries on the agentless machine are not displayed on the MOM Management Server unless it has the same EventLogmessages.dll file as the agentless computer. A workaround is to install the software for which you'd like to receive event log entries on the MOM server.
-
Agentless monitoring does not work through a firewall in typical configurations because agentless network traffic contains remote procedure call (RPC) and Distributed Component Object Model (DCOM).
-
Not all management packs work in agentless mode. Therefore, it might not make operational sense for your management pack to work without an agent if the bulk of the monitoring scenarios leverage providers that are not supported without an agent.
Because agents are core to the MOM architecture and in general provide more functionality, it probably makes sense to use them whenever possible. However, for those cases where an agent cannot be deployed to the remote system, agentless monitoring remains an option.